Это старая редакция страницы Библиотека / Статьи / Certified Lies / Certificate Authoritiesandthe Browser Vendors за 25/03/2010 16:25.
2. Удостоверяющие центры и поставщики браузеров
2 Certificate Authorities and the
In this section, we provide a brief overview of the
roles played by the Certificate Authorities in the
public key infrastructure, the browser vendors in
picking the certificate authorities that they include
in the browsers, and existing man-in-the-middleattack techniques that circumvent SSL based security.
В этом разделе мы представим краткое рассмотрение роли, играемой удостоверяющими центрами в инфраструктуре открытых ключей, выборе сертификатов поставщиками браузеров, которые они вэти браузеры затем и включают и существующие методики атак человека посредине для обхода безопасности, основанной на SSL.
2.1 Certificate Authorities
2.1 Удостоверяющие центры сертификатов
CAs play a vital role in the SSL public key infrastructure (PKI).
Each CA's main responsibility is to verify the identity of the entity to which it issues a certificate.1
УЦ играют важную роль в инфраструктуре открытых ключей — public key infrastructure (PKI) для SSL. Главная обязанность каждого УЦ — проверка идентичности субъекта, которому выдаётся сертификат.
upon the type of certificate purchased. A domain registration
certificate can be obtained for less than $15, and will typi-
cally only require that the requester be able to reply to an
email sent to the administrative address listed in the WHOIS
database. Extended Validation (EV) certificates require a
greater de of verification.
Уровень проверки, осуществляемой УЦ зависит от типа выдаваемого сертификата. Регистрация сертификата на домен можен быть получена менее чем за 15$ и обычно требует только чтобы запрашивающий был способен послать имэйл к административному адресу, находящемуся в списке базы данных WHOIS. Расширенная проверка (Extended Validation — EV) требует более сложных методов.
Thus, when a user visits https:
//www.bankofamerica.com, her browser will inform
her that the bank's certificate is valid, was issued
by VeriSign, and that the website is run by Bank of
America. It is because of the authenticity and confidentiality guaranteed by SSL that the user can continue with her transaction without having to worry
that she is being phished by cyber-criminals.
Таким образом, когда пользователь посещает https://www.bankofamerica.com, браузер будет информировать его о том, что банковский сертификат действителен, выдан компанией VeriSign и этот сайт запущен компанией Bank of America. Таким образом аутентичность и конфиденциальность гарантирована
Those trusted by the browsers ("root CAs"), those
trusted by one of the root CAs ("intermediate
CAs"), and those neither trusted by the browsers
nor any intermediate CA ("untrusted CAs"). Fur-
thermore, intermediate CAs do not necessarily have
to be directly verified by a root CA — but can be
verified by another intermediate CA, as long as the
chain of trust eventually ends with a root CA.
intermediate CAs are functionally equivalent. A
website that presents a certificate signed by either
form of CA will cause the users' browser to display
a lock icon and to change the color of the location
bar. Whereas certificates verified by an untrusted
CA and those self-signed by the website owner will
result in the display of a security warning, which
for many non-technical users can be scary [3], con-
fusing, and difficult to bypass in order to continue
navigating the site [4].
is currently implemented, all root CAs are equally
trusted by the browsers. That is, each of the 264
root CAs trusted by Microsoft, the 166 root CAs
trusted by Apple, and the 144 root CAs trusted
by Firefox are capable of issuing certificates for any
website, in any country or top level domain [5]. For
example, even though Bank of America obtained its
current SSL certificate from VeriSign, there is no
technical reason why another CA, such as GoDaddy,
cannot issue another certificate for the same site to
someone else. Should a malicious third party some-
how obtain a certificate for Bank of America's site
and then trick a user into visiting their fake web
server (for example, by using DNS or ARP spoof-
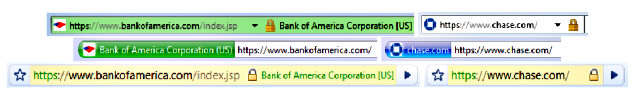
Figure 1: The browser location bars of Internet Explorer (top), Firefox (middle) and Chrome (bottom)
when visiting an Extended Validation HTTPS site (Bank of America) and a site with a standard HTTPS
certificate (Chase). Note that the country information ("US") presented by the browsers refers to the
corporation that obtained the certificate (Bank of America), not the location of the Certificate Authority.
ing), there is no practical, easy way for the user to
determine that something bad has happened, as the
browser interface will signal that a valid SSL session
has been established.2
knowingly provide such a certificate to a malicious
third party. Doing so would almost certainly lead
to significant damage to its reputation, a number of
lawsuits, as well as the ultimate threat of having its
trusted status revoked by the ma jor web browsers.3
Therefore, it is in each CAs' self-interest to ensure
that malicious parties are not able to obtain a cer-
tificate for a site not under their own control.
restrictions in place that prohibit a CA from issuing
a certificate to a malicious third party. Thus, both
the integrity of the CA based public key infrastruc-
ture and the security users' communications depend
upon hundreds of CAs around the world choosing to
do the right thing. Unfortunately, as will soon be
clear, any one of those CAs can become the weakest
link in the chain.
formation listed in the browser's SSL interface, she will still
lack the information necessary to make an informed trust de-
cision. Since GoDaddy is a valid certificate authority and has
issued millions of other valid certificates, there is no way for
the user to determine that any one particular certificate was
improperly issued to a malicious third party.
over each CA. Any CA no longer trusted by the ma jor
browsers will have an impossible time attracting or retaining
clients, as visitors to those clients' websites will be greeted by
a scary browser warning each time they attempt to establish a
secure connection. Nevertheless, the browser vendors appear
loathe to actually drop CAs that engage in inappropriate be-
havior — a rather lengthy list of bad CA practices that have
not resulted in the CAs being dropped by one browser vendor
can be seen in [6].
Назад | Оглавление | Дальше